
Call center compliance checklist
Stay compliant with our call center compliance checklist. Learn about network security, data protection, PCI DSS, and more!

A comprehensive call center security checklist to help you protect customer data, prevent breaches, and ensure compliance with security standards.
Are you confident that your call center is secure? If not, go through this call center security checklist.
We will discuss the most important security measures that you need to take in order to protect your business. We’ll cover everything from password protection to data encryption. By following our tips you can rest assured that your call center will be safe from hackers and other external threats.
A call center is a critical part of any business. It’s the lifeline that connects you to your customers and clients. And, like any other important asset, it needs to be protected.
That’s why we’ve put together this call center security checklist. It will help you identify any weak points in your contact center’s security, as well as providing call center security tips on how to fix them.
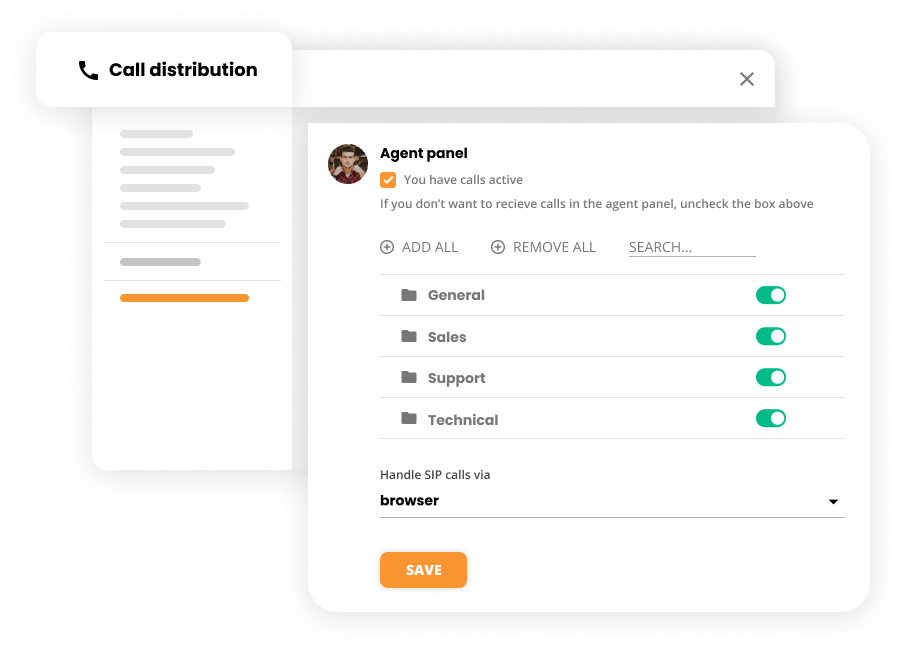
Strong access control measures are essential for any call center. They help you prevent unauthorized access to your system and data. Multi-factor authentication, single sign-on, and role-based access control are all great options to consider.
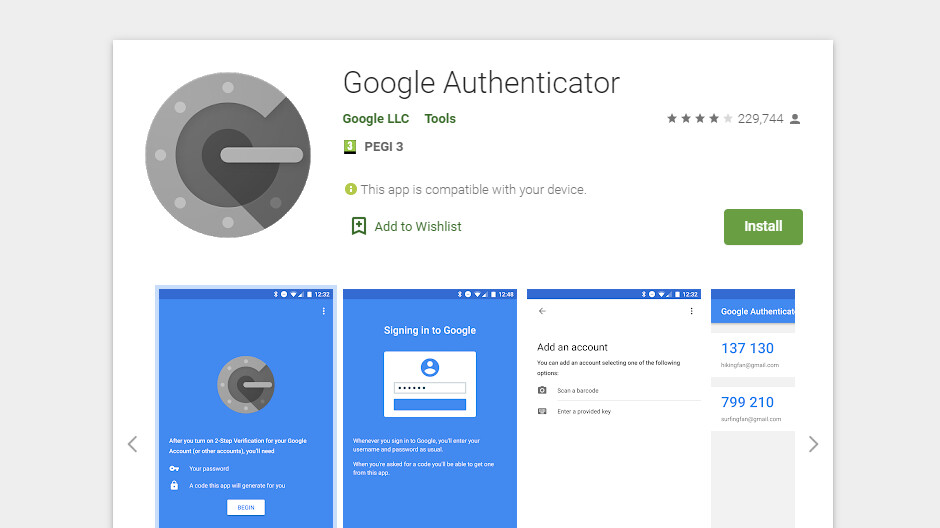
Multi-factor authentication adds an extra layer of security. This makes it more difficult for hackers to gain access to your system.
A multi-factor authentication system requires users to provide more than one piece of evidence in order to confirm their identity. Single sign-on allows users to log in with one set of credentials instead of multiple sets. Role-based access control restricts users to only the areas and data they need to access.
Customer service representatives have access to sensitive customer data. That’s why it’s important to limit the levels of access to their privileges.
It helps you prevent unauthorized access to sensitive customer data and prevent them from leaking out of the company.
Restrict access to certain areas of the call center. Limit the amount of time an agent can spend in each area. Monitor agent activity and flag any suspicious behavior.
Insisting on regular password changes is an elementary security measure.
Regularly changing passwords help prevent unauthorized access to your system. It also helps protect your data in the event that a password is leaked or stolen.
You can use a password management tool that will generate and store passwords for you. You can also set up your own password rotation schedule. For example, you could require users to change their passwords every 30 days. They should also change default passwords immediately.
How often should passwords be changed? Most experts recommend changing them every 3 to 6 months. If, however, you have a lot of sensitive information, you may need to change your password more frequently.
In the event of a security breach, you wouldn’t want to be without access to your logs or IP addresses .
Accessing logging and IP addresses history helps you track down the source of a problem and prevent it from happening again.
Use a secure cloud-based service that stores logs and IP addresses. This will enable you to access them from anywhere and keep them properly stored. You can also use an on-premises solution, but they’re usually more expensive.
One of the most common ways for malware to find its way onto a computer is through programs that are installed without the user’s knowledge.
It allows you to prevent unauthorized access to your system and data, and it protects your company from liability if a program containing malware is installed.
As a call center manager, you should establish strict rules for installing programs on company computers. Employees should only be allowed to install programs that are necessary for their job duties. All other programs should be prohibited.
Additionally, all programs should be installed by the IT department to ensure that only authorized programs are installed on company computers. Also use an application whitelist, allowing you to specify which applications can be installed on your system, and blacklist, defining those that are blocked.

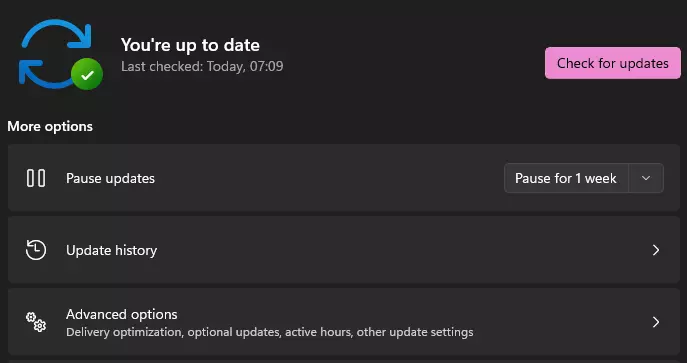
One of the best ways to prevent security breaches is to keep all systems up-to-date.
Regular updates help you close any security loopholes that may exist. It also helps to protect your system from new security threats that may have emerged since the last update.
Use automatic updates or you can update your system manually. In that case, it’s vital to not forget to do so on a regular basis – pay great attention to this.
Regularly reviewing your network rules is an important part of keeping your call center secure.
It helps you identify any potential security risks and take steps to mitigate them.
Conduct a security audit of your network on a regular basis. This should include a review of your firewall rules, access control lists, and other security settings.
All call center employees should receive training on security and compliance policies.
It helps ensure that all employees are aware of the security risks and know how to protect themselves and the company.
Create a training program that covers all of the relevant security and compliance topics. This should include information on how to identify and report security threats, as well as what to do in the event of a breach.
Gamification is a great way to encourage employees to learn about security and compliance.
It helps keep employees engaged and motivated to learn about security best practices.
LiveAgent offers gamification features that can be used to encourage employees to learn about security. This includes badges, leaderboards, and rewards for completing training modules.
A knowledge base is a valuable resource for call center employees. It should be kept secure to prevent unauthorized access.
It helps protect sensitive information and ensures that only authorized employees have access to it.
Use access controls to restrict who can view and edit the knowledge base. Regularly review the content to ensure that it is up-to-date and accurate.
If your call center handles credit card transactions, you need to ensure that cardholder data is protected.
It helps prevent fraud and protects your customers’ financial information.
Comply with PCI DSS (Payment Card Industry Data Security Standard) requirements. This includes encrypting cardholder data, using secure payment processing systems, and regularly testing your security measures.
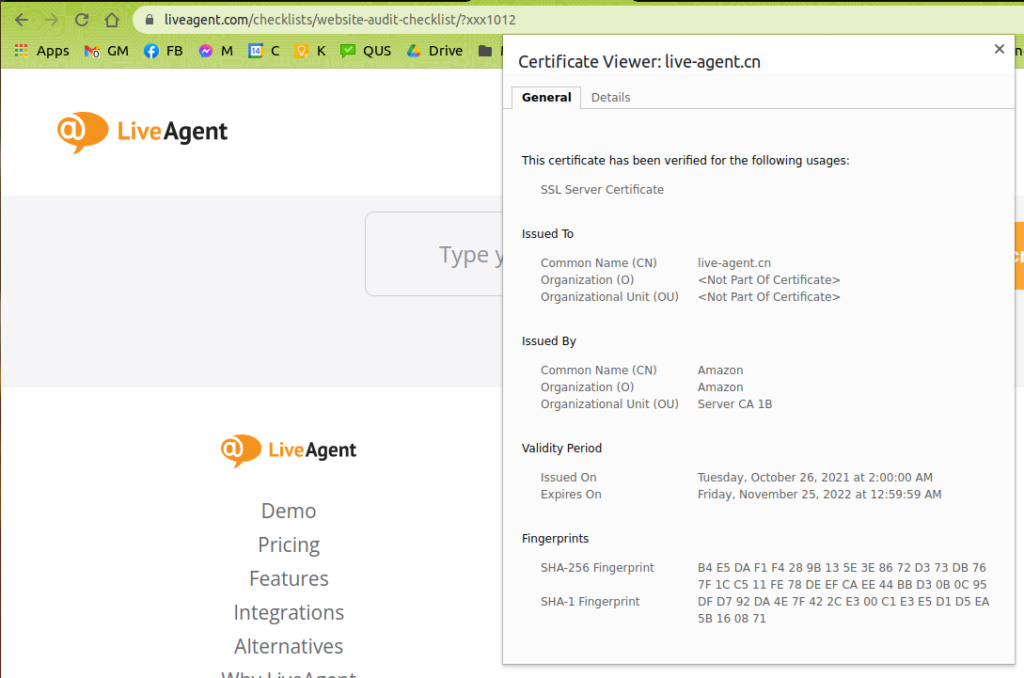
Keeping your call center software up-to-date with the latest security measures is vital.
Call center software must be compliant with the latest security measures in order to protect your call center’s data.

When you are selecting the call center software , check with the software service provider if they have any compliance certification. Data security should be a top priority for the company.
Ask industry experts if they recommend this software for call centers and read online reviews to see if other call center professionals have had good experiences with it. Alternatively, you can always contact a call center security consultant to get their opinion on the best way to verify compliance.
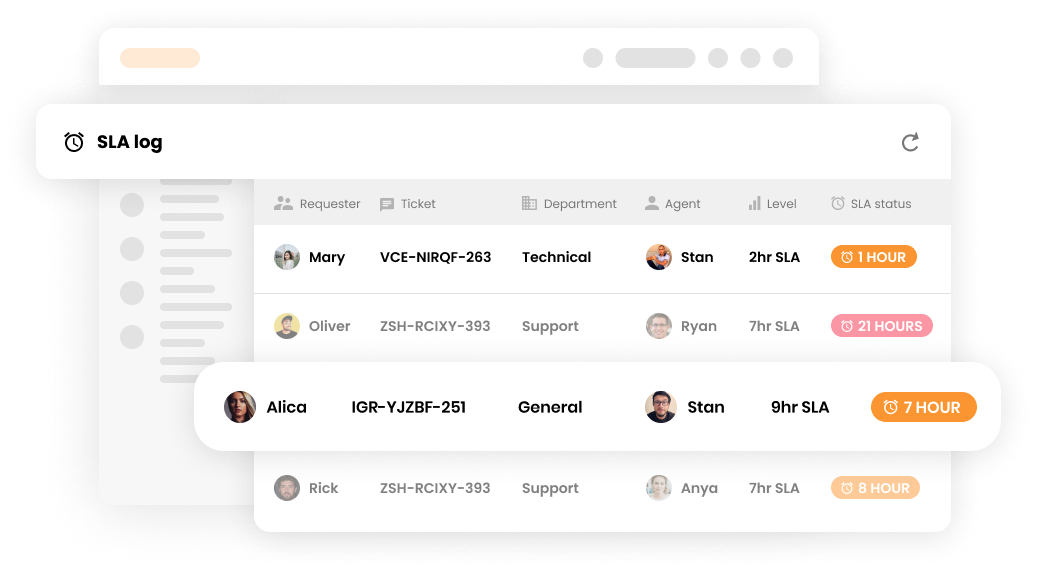
Real-time alerts will help you detect and investigate suspicious activity quickly and prevent data leaks.
By being alerted immediately about any unauthorized access, you can take steps to prevent a breach from occurring.
Check with your call center software provider to see if they offer any security features that include notifications about unauthorized access. You can also set up a separate notification system using a tool like IFTTT for this purpose, or have your IT team set up alerts to notify you about any unauthorized access.
Human error is one of the leading causes of data breaches. By automating as many of your call center processes as possible, you can help eliminate potential security risks.
By automating call center tasks , you increase the chances of them being completed correctly and securely. It also helps free up your employees’ time so that they can focus on other tasks to improve your call center’s efficiency.

Determine which tasks your contact center agents need to spend the most time on and if they can be automated. Some tasks, such as customer service or sales, can’t be automated entirely. However, you can still use automation for parts of the process, such as follow-ups or appointment scheduling.
For example, in LiveAgent, you can automate call routing by priority or make use of automatic callback . Additionally, you can set up automation rules in the help desk to transfer tickets to specific departments, add tags, mark tickets as spam, or resolve them.
There are many accepted security frameworks out there such as ISO 27001, NIST 800-53, and COBIT.
It allows you to follow a set of security guidelines that are already tried and tested. This also makes it easier for other businesses to understand your security stance and for auditors to assess your compliance.
The first step is to identify which framework is most relevant to your business. Once you have done that, you can begin to map out the strict security controls required by the framework and implement them in your call center.
If your call center provides international services then you must be aware of the different data and privacy standards that exist in each country, e.g. GDPR .
Data and privacy standards vary from country to country, so it’s important to ensure that you comply with the standards in the places that you operate in to avoid any penalties.
The best way to do this is to consult with a lawyer or compliance specialist who is familiar with the standards of the countries you operate in. You shouldn’t rely on general advice from the internet, as the standards can change and the information that you find might not be up to date.

End-to-end encryption is a security measure that encrypts data at the source (the sender) and decrypts it only at the destination (the receiver).
Doing so ensures that only the sender and the receiver can access the data, and prevents intermediate parties from decrypting or reading them.
You will need to choose an end-to-end encryption solution that is compatible with your call center software . Once you have picked one, you can start encrypting calls made through your call center.
Hackers are constantly finding new ways to exploit security vulnerabilities in systems, and call centers are no exception. In fact, they may be even more vulnerable than other businesses because of the nature of their work.
One of the biggest threats to call center security is data leakage. This can happen in a number of ways, such as an employee accidentally emailing sensitive information to the wrong person, or hackers gaining physical access to systems and stealing data. So, how can you protect the company?
Educate employees on the importance of security and handling sensitive information correctly. Implement strict policies and procedures for handling sensitive data. Use data encryption to protect information, both in transit and at rest. Regularly monitor systems for signs of unauthorized access.
Another big threat to call center security is unsegmented networks, meaning that which is used by the call center is not segregated from the rest of the company’s network. This can be a problem because a security breach in another part of the network can also affect the call center.
For this reason, it’s important to segment the call center from the rest of the company’s network by firewalls or virtual private networks (VPNs).
It’s also important to have security policies and procedures in place that restrict access to the call center network. Only authorized personnel should have access, and they should only be able to do so from approved locations.
Phishing is a type of cyber attack that involves hackers sending fraudulent emails or messages in an attempt to deceive people into giving them sensitive information. This can be a problem for call centers because employees may be tricked into giving hackers access to the system.
To help protect against phishing attacks, it’s important to educate employees on how to spot them. It’s also a good idea to implement security measures such as two-factor authentication, which makes it more difficult for hackers to gain access to systems.
Social engineering schemes are becoming increasingly sophisticated, and call center employees are often the first line of defense against such attacks. Hackers exploit social engineering schemes to trick employees into divulging sensitive information or giving them access to the system.
Education is the best way to protect against social engineering attacks. Employees should be aware of red flags such as unexpected requests for information or calls from unfamiliar numbers.
Ransomware and malware are both types of malicious software that may be used to attack call centers. Ransomware can be used to encrypt sensitive data and demand a ransom for the decryption key, while malware can be used to disable systems or steal data.
Implementing security measures such as encryption and regular backups can help prevent these types of attacks. It’s also a good idea to have a security policy in place that requires employees to report any suspicious emails or messages.

Stay compliant with our call center compliance checklist. Learn about network security, data protection, PCI DSS, and more!

Streamline your call center setup with our ultimate checklist! Learn goals, tools, onboarding, and tips for success. Start now!

Comprehensive call center requirements checklist covering software, internet, equipment, technology, CRM, calling features, staff, compliance, security, and mor...
Cookie Consent
We use cookies to enhance your browsing experience and analyze our traffic. See our privacy policy.