
Call center security checklist
Secure your call center with our comprehensive security checklist. Learn about access control, encryption, compliance, and more!

A comprehensive call center compliance checklist to help you stay up-to-date with legal requirements and protect customer data.
As a business owner, you will know the importance of compliance with applicable laws and regulations. Call centers that keep many sensitive customer records are especially at risk. How to maximize help desk security ?
Here’s how: by following a handy checklist of call center compliance requirements. By completing it, you will help keep your call center safe.
It’s a tool that helps all kinds of contact centers to stay up-to-date with the latest legal requirements. By ensuring that your agents adhere to the rules listed below, you can reduce the risk of fines or other penalties.
A call center compliance checklist can be used by businesses of all sizes. Our checklist will help your business obey the law whether it is a small one with a single contact center or an enterprise with multiple call centers .
This is the backbone of your compliance program. Without a secure network, all of your call center ’s operations are open to danger.
Because it helps protect your customer data from unauthorized access, theft, or modification.
If you’re not sure where to start, consider working with an IT security consultant. It can be done in two ways:
Tip: for more information on building and sustaining a secure network infrastructure, consult the National Institute of Standards and Technology (NIST).

Web services are heavily subjected to malware targeting. Credit card transactions are not an exception, so contact centers also need to be protected against those. The development of such a program is a proactive approach to managing cyber threats and vulnerabilities.
It helps you identify, prioritize, and remediate security issues before they become problems for your business or customers. Such a program can also tell you exactly what you need to do in case of a security breach.

Protected access to cardholder data refers to any information about a customer that’s stored on your system. This can include names, addresses, phone numbers, credit card numbers, and more.
It prevents hackers from gaining access to cardholder information and using it to commit fraud or identity theft. Additionally, it prevents any unauthorized transmission of cardholder data.

First, make sure you’re compliant with The Payment Card Industry Data Security Standard (PCI DSS standard) requirements. Then, implement a strong access control measure to protect the private details of your clients.
Tip: avoid storage of customer details and remove any previously kept data.
A powerful cryptographic system and encryption are needed to ensure that sensitive cardholder data is transmitted securely.
This is a document that outlines an organization’s approach to protecting its electronic information.
It provides a framework for employees to follow when handling sensitive data and thus helps protect the business.

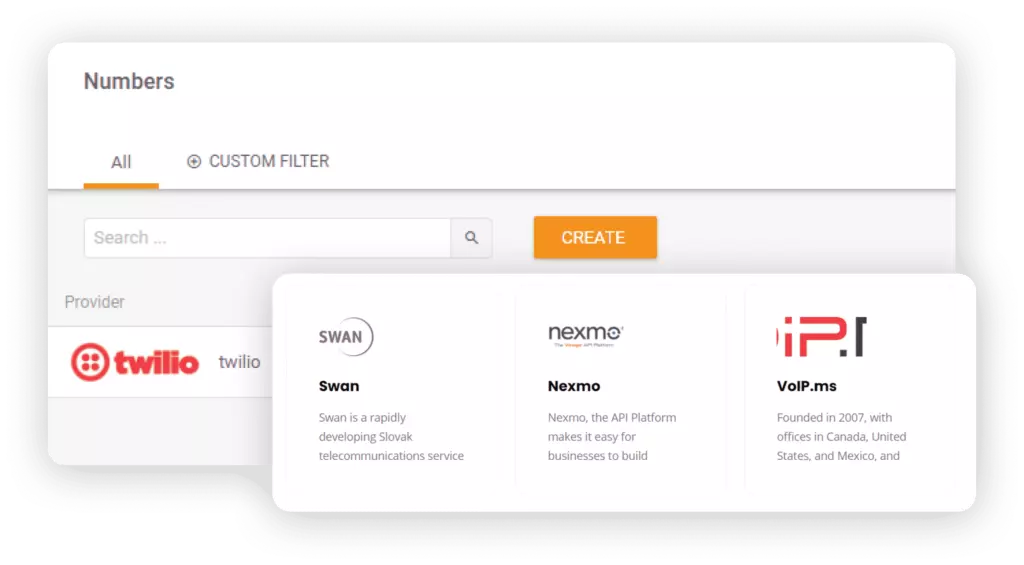
Access control is a process that lets you manage who has access to your systems and data. Selecting a help desk software that has all of the latest security capabilities is imperative here.
It protects your data from unauthorized access, reduces the risk of internal fraud and abuse, and helps protect customer privacy.
The key is to choose automated help desk software such as LiveAgent to control all measures on your behalf. It’s a solution that helps you safely manage all your customer inquiries from one interface.

By choosing such a tool, you will increase the security of your customers’ data. LiveAgent provides:
You can test LiveAgent out for free before making any financial commitments.
Encryption is a process of converting data into ciphertext so that it can only be accessed by those who have the decryption key.
Doing so assures customers that information being transmitted is protected from eavesdropping and other forms of interception.
There are several different encryption protocols that can be used, such as Secure Sockets Layer (SSL) and Transport Layer Security (TLS), both crucial for maintaining cybersecurity compliance in voice transactions.
Tip: if you are using LiveAgent’s help desk , you can take advantage of its built-in encryption. LiveAgent encrypts all data by default via SSL (HTTPS) and TLS, so all the traffic between your website/application and our servers is secure.
To prevent any fraudulent activity, it’s important not to allow access to customer payment information.
Not allowing access helps protect your customers’ financial details from being stolen by cybercriminals.
First, make sure your employees are aware of their responsibilities regarding sensitive data protection. Use strong authentication procedures such as two-factor authentication and one-time passwords. Also, encrypt all data transmissions between payment terminals and servers so that no one can intercept them in transit.
If you must keep track of this data, make certain that it is stored in a secure location and that access is limited to authorized personnel only.
Doing so is not in compliance with GDPR law and makes it easy for unauthorized individuals to access this information.
If you must take notes, make sure to use a secure method of storing them. This could include locking away notebooks in a safe or using an encrypted file storage system.

The use of mobile phones in a contact center increases the risk of data loss or theft.
It reduces the chances of sensitive information being lost or stolen due to an employee error such as losing their device.
Educate your employees on the cyber security risk associated with using a personal device and make sure they understand the importance of data security. Require employees to password-protect their devices and install reputable security apps. Make sure that all sensitive data is encrypted before being stored or transmitted on a mobile device.

This is one of the best ways to identify vulnerabilities before they become a problem for your organization or customers.
It helps you prevent unauthorized access, data loss, or theft from hackers who might be trying to get into your system through weaknesses and gaps that haven’t yet been discovered.

Install a network security monitoring tool to keep track of all activity. Set up alerts so that you can be notified of any suspicious activity that occurs in real-time. Regularly test the security of your networks by running vulnerability scans and penetration tests.
Personal data threats - One of the most common dangers in a contact center is the risk of data theft or loss. Agents are privy to a great deal of personal information, including social security numbers, bank account details, and credit card numbers. As such, it’s important that all agents receive adequate employee training on how to safely store and transmit this data.
Internal threats - Call center agents may pose a risk to the center if they have access to sensitive information and become disgruntled. It’s important to regularly monitor agent activity and to have policies in place that restrict access to certain data.
Temporary employees - Call centers often employ temporary workers to handle peak volumes or cover for sick employees. It’s important to take steps to ensure that these workers are trained on the center’s policies and procedures and that they understand the risks associated with working in a call center, otherwise they may inadvertently compromise its security.
Accidental clicks - Sometimes employees click on links or open files that they shouldn’t, leading to the installation of malware or the theft of data. It is essential to have safeguards in place against such mistakes, such as strong password protection and security software.
An employee with a grudge - An employee with a grudge against the company or another agent can do a great deal of damage. For example, they could leak sensitive data, sabotage systems, or harass other employees. It’s important to monitor employee activity closely and have policies in place to deal with such situations.
External threats - Hackers and scammers from outside the organization can use phishing or other techniques to try to steal information or install malware on call center computers. The best way to protect against these threats is to implement strong security measures such as firewalls, antivirus software, and spam filters.

Secure your call center with our comprehensive security checklist. Learn about access control, encryption, compliance, and more!

Streamline your call center setup with our ultimate checklist! Learn goals, tools, onboarding, and tips for success. Start now!

Comprehensive call center requirements checklist covering software, internet, equipment, technology, CRM, calling features, staff, compliance, security, and mor...
Cookie Consent
We use cookies to enhance your browsing experience and analyze our traffic. See our privacy policy.